MC801A Firmwares
Firmwares (using google translate):
PLKPLMC801AV1.0.0B03 – Polish (Play operator). Web interface password:admin. Fully compatible with 5G networks (channel n 78 ), the speed does not slow down . The firmware is not updated via the web interface; the firmware update is conditioned by the presence of an original SIM card from the operator
SASTCMC801AV1.0.0B05 – Saudi (STC operator).
–Patch 1 (for upgrading B05 to B06 version via computer): DL_MC801A_STC_SAV1.00.01
–Patch 2 (for upgrading B05 to B07 version via computer): DL_MC801A_STC_SAV1.00.02
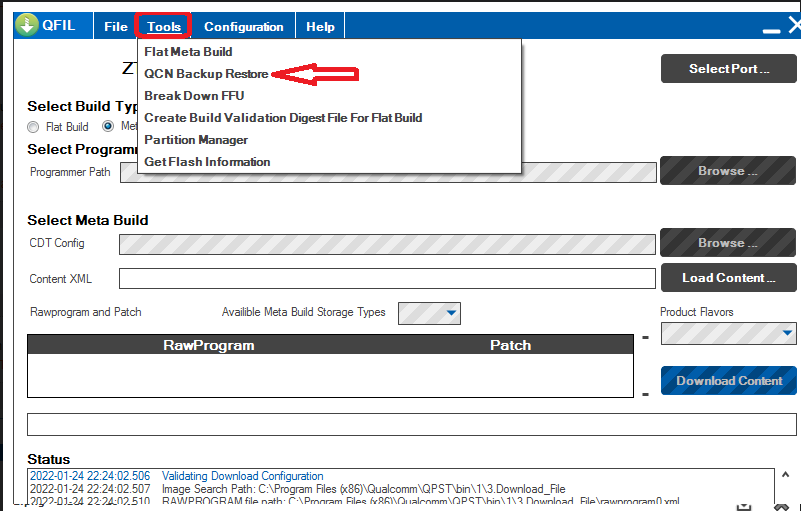
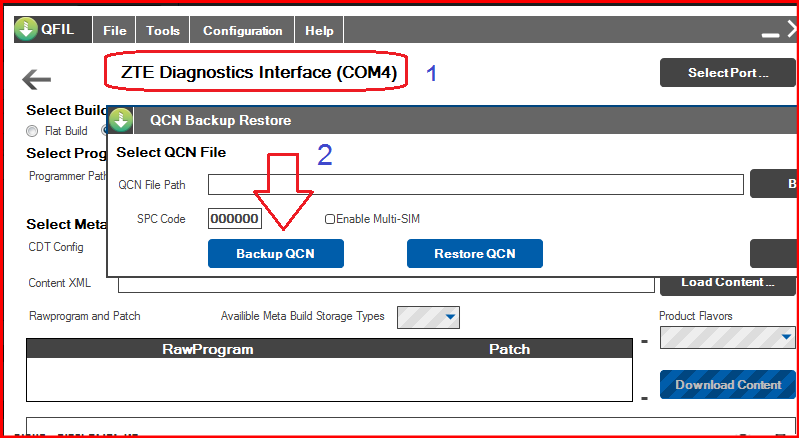
NEW: Saudi firmwareB07(STC operator)ZTE_STC_BD_SASTCMC801AV1.0.0B07 (sew via QFIL, after unpacking, the archive contains folder number 3, no other folders are needed for flashing) There is a firmware update in the web interface , the N78 (5G) channel does not work.
NEW: firmware ZAMTNMC801AV1.0.0B01 (South Africa, MTN operator) Fully compatible with 5G networks (channel n 78 ) speed does not decrease. The firmware is not updated via the web interface; the firmware update is conditioned by the presence of an original SIM card from the operator
TMOPLMC801AV1.0.0B07 – Polish (T-Mobile operator). Web interface password:admin. Fully compatible with 5G networks (channel n 78) speed does not cut . The firmware is not updated via the web interface; the firmware update is conditioned by the presence of an original SIM card from the operator
ATH3GMC801AV1.0.0B08 – Austrian (operator DreiMAXX) – Three . The firmware is not updated via the web interface, the firmware update is due to the presence of an original SIM card from the operator , the N78 (5G) channel does not work.
CNHKMC801AV1.0.0B11 – Hong Kong (SmarTone operator). Fully compatible with 5G networks (channel n 79 ), the speed does not slow down . There is a firmware update in the web interface , the N78 (5G) channel does not work.
FITELIAMC801AV1.0.0B12– Scandinavia (operator Telia), Webcam address http://192.168.32.1 , There is a firmware update in the web interface , the N78 (5G) channel does not work.
MC801A_Elisa2_B13 – Finnish (Elisa operator), Webcam address http://192.168.100.1 , The firmware is not updated via the web interface, the firmware update is due to the presence of an original SIM card from the operator , the N78 (5G) channel does not work.
CNCNLMC801AV1.0.0B12 – Mainland China, blocked frequency aggregation (no LTE CA).
CNCNLMC801AV1.0.0B18 – Mainland China, blocked frequency aggregation (no LTE CA).
CNCNLMC801AV1.0.0B22– Mainland China, blocked frequency aggregation (no LTE CA). There is an update in the web interface for firmware B33. Fully compatible with 5G networks on channel n 78 , the speed does not cut down, but it is necessary to select the carrier frequency B3 (4G) in Debug Page
NEW: : CN_CMIOT_MC801AV1.0.0B02 – China, operator, the largest operator in China “China Mobile” blocked frequency aggregation (without LTE CA). Fully compatible with 5G networks on channel n 78 , the speed does not slow down, but you need to select the carrier frequency B3 (4G) in Debug Page The firmware is not updated via the web interface.
NEW: : BD_CNBGBJMC801AV1.0.0B06 – China, Beijing region, blocked frequency aggregation (without LTE CA). Fully compatible with 5G networks on channel n 78 , the speed does not slow down, but you need to select the carrier frequency B3 (4G) in Debug Page The firmware is not updated via the web interface.
Source: https://4pda.to/forum/index.php?showtopic=1011903&st=100#entry107391391